Ruby Generate Rsa Key Pair
- Generate Rsa Key Pair Online
- Ruby Generate Rsa Key Pair Test
- Generate Rsa Public Key
- How To Generate Rsa Key
I suggest you try out the key generation utilities ssh has to offer. There is one particular tool called ssh-keygen which allows you to create a public/private key pair. Github actually has an easy to understand article explaining how to generate these keys. Once you generate your key pair, you can use your public key to encrypt messages using a PKCS 1.5 algorithm and decrypt the messages. Once keys are generated, we can use ToXmlString or ExportParameters method to read the keys. The ToXmlString method returns key information in XML as a string. The method takes a Boolean parameter. If passed false, it returns public key only. If passed true, it returns both private and public pair. The following code snippet returns a public key.
Several tools exist to generate SSH public/private key pairs. The following sections show how to generate an SSH key pair on UNIX, UNIX-like and Windows platforms.
Generating an SSH Key Pair on UNIX and UNIX-Like Platforms Using the ssh-keygen Utility
UNIX and UNIX-like platforms (including Solaris and Linux) include the ssh-keygen utility to generate SSH key pairs.
$ openssl rsa -pubout -in privatekey.pem -out publickey.pem writing RSA key A new file is created, publickey.pem, with the public key. It is relatively easy to do some cryptographic calculations to calculate the public key from the prime1 and prime2 values in the public key file. However, OpenSSL has already pre-calculated the public key. Implements RSA key pair generation using Ruby's OpenSSL standard library. Compatible with Ruby 1.9.1+ and JRuby 1.5.0+. Compatible with older Ruby versions with the help of the Backports gem. Examples require 'rsa' Generating a new RSA key pair keypair = RSA::KeyPair.generate(128) Encrypting a plaintext message. It is in widespread use in public key infrastructures (PKI) where certificates (cf. OpenSSL::X509::Certificate) often are issued on the basis of a public/private RSA key pair. RSA is used in a wide field of applications such as secure (symmetric) key exchange, e.g. When establishing a secure TLS/SSL connection. It is also used in various digital signature schemes.
- Navigate to your home directory:
- Run the ssh-keygen utility, providing as
filenameyour choice of file name for the private key:The ssh-keygen utility prompts you for a passphrase for the private key.
- Enter a passphrase for the private key, or press Enter to create a private key without a passphrase:
Note:
While a passphrase is not required, you should specify one as a security measure to protect the private key from unauthorized use. When you specify a passphrase, a user must enter the passphrase every time the private key is used.
The ssh-keygen utility prompts you to enter the passphrase again.
- Enter the passphrase again, or press Enter again to continue creating a private key without a passphrase:
- The ssh-keygen utility displays a message indicating that the private key has been saved as
filenameand the public key has been saved asfilename.pub. It also displays information about the key fingerprint and randomart image.
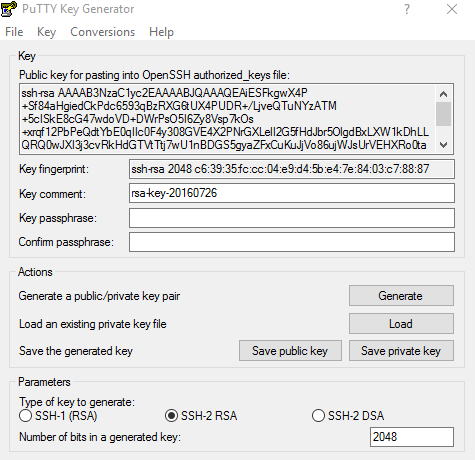
Generating an SSH Key Pair on Windows Using the PuTTYgen Program
The PuTTYgen program is part of PuTTY, an open source networking client for the Windows platform.
- Download and install PuTTY or PuTTYgen.
To download PuTTY or PuTTYgen, go to http://www.putty.org/ and click the You can download PuTTY here link.
- Run the PuTTYgen program.
- Set the Type of key to generate option to SSH-2 RSA.
- In the Number of bits in a generated key box, enter 2048.
- Click Generate to generate a public/private key pair.
As the key is being generated, move the mouse around the blank area as directed.
- (Optional) Enter a passphrase for the private key in the Key passphrase box and reenter it in the Confirm passphrase box.
Note:
While a passphrase is not required, you should specify one as a security measure to protect the private key from unauthorized use. When you specify a passphrase, a user must enter the passphrase every time the private key is used.
- Click Save private key to save the private key to a file. To adhere to file-naming conventions, you should give the private key file an extension of
.ppk(PuTTY private key).Note:
The.ppkfile extension indicates that the private key is in PuTTY's proprietary format. You must use a key of this format when using PuTTY as your SSH client. It cannot be used with other SSH client tools. Refer to the PuTTY documentation to convert a private key in this format to a different format. - Select all of the characters in the Public key for pasting into OpenSSH authorized_keys file box.
Make sure you select all the characters, not just the ones you can see in the narrow window. If a scroll bar is next to the characters, you aren't seeing all the characters.
- Right-click somewhere in the selected text and select Copy from the menu.
- Open a text editor and paste the characters, just as you copied them. Start at the first character in the text editor, and do not insert any line breaks.
- Save the text file in the same folder where you saved the private key, using the
.pubextension to indicate that the file contains a public key. - If you or others are going to use an SSH client that requires the OpenSSH format for private keys (such as the
sshutility on Linux), export the private key:- On the Conversions menu, choose Export OpenSSH key.
- Save the private key in OpenSSH format in the same folder where you saved the private key in
.ppkformat, using an extension such as.opensshto indicate the file's content.
Contents
- 3. Saving the Keys in Binary Format
- Source Code
1. Introduction
Let us learn the basics of generating and using RSA keys in Java.
Generate Rsa Key Pair Online
Java provides classes for the generation of RSA public and private key pairs with the package java.security. You can use RSA keys pairs in public key cryptography.
Public key cryptography uses a pair of keys for encryption. Distribute the public key to whoever needs it but safely secure the private key.
Public key cryptography can be used in two modes:
Encryption: Only the private key can decrypt the data encrypted with the public key.
Authentication: Data encrypted with the private key can only be decrypted with the public key thus proving who the data came from.
2. Generating a Key Pair
First step in creating an RSA Key Pair is to create a KeyPairGeneratorfrom a factory method by specifying the algorithm (“RSA” in this instance):
Initialize the KeyPairGenerator with the key size. Use a key size of 1024 or 2048. Currently recommended key size for SSL certificates used in e-commerce is 2048 so that is what we use here.
From the KeyPair object, get the public key using getPublic() and the private key using getPrivate().
3. Saving the Keys in Binary Format
Save the keys to hard disk once they are obtained. This allows re-using the keys for encryption, decryption and authentication.
What is the format of the saved files? The key information is encoded in different formats for different types of keys. Here is how you can find what format the key was saved in. On my machine, the private key was saved in PKCS#8 format and the public key in X.509 format. We need this information below to load the keys.
3.1. Load Private Key from File
After saving the private key to a file (or a database), you might need to load it at a later time. You can do that using the following code. Note that you need to know what format the data was saved in: PKCS#8 in our case.
3.2 Load Public Key from File
Load the public key from a file as follows. The public key has been saved in X.509 format so we use the X509EncodedKeySpec class to convert it.
4. Use Base64 for Saving Keys as Text
Save the keys in text format by encoding the data in Base64. Java 8 provides a Base64 class which can be used for the purpose. Save the private key with a comment as follows:
And the public key too (with a comment):
5. Generating a Digital Signature
As mentioned above, one of the purposes of public key cryptography is digital signature i.e. you generate a digital signature from a file contents, sign it with your private key and send the signature along with the file. The recipient can then use your public key to verify that the signature matches the file contents.
Here is how you can do it. Use the signature algorithm “SHA256withRSA” which is guaranteed to be supported on all JVMs. Use the private key (either generated or load from file as shown above) to initialize the Signatureobject for signing. It is then updated with contents from the data file and the signature is generated and written to the output file. This output file contains the digital signature and must be sent to the recipient for verification.
Ruby Generate Rsa Key Pair Test
6. Verifying the Digital Signature
Generate Rsa Public Key
The recipient uses the digital signature sent with a data file to verify that the data file has not been tampered with. It requires access to the sender’s public key and can be loaded from a file if necessary as presented above.
The code below updates the Signature object with data from the data file. It then loads the signature from file and uses Signature.verify() to check if the signature is valid.
Gpg key generator once more f ram. And that in a nutshell is how you can use RSA public and private keys for digital signature and verification.
Source Code
How To Generate Rsa Key
Go here for the source code.