Putty Generate Ssh Key Linux
Generate RSA keys with SSH by using PuTTYgen
One effective way of securing SSH access to your cloud server is to usea public-private key pair. This means that a public key is placed onthe server and a private key is placed on your local workstation.Using a key pair makes it impossible for someone to log in by using justa password, as long as you set up SSH to deny password-basedauthentication.
- Jul 19, 2013 PuTTYgen is what you will use to generate your SSH keys for use in PuTTY. To start, all you need to do is download the exectuable files (.exe) and save them on the computer that you'll use to connect to your VPS, e.g. On the desktop.
- PuTTYgen is a key generator tool for creating pairs of public and private SSH keys. It is one of the components of the open-source networking client PuTTY. Although originally written for Microsoft Windows operating system, it is now officially available for multiple operating systems including macOS, Linux.
- Red Hat Enterprise Linux (RHEL) 6.3; Issue. SSH Keys generated by Putty do not work with openssh in Red Hat Enterprise Linux; Resolution. To make it working convert the keys generated by Open-ssh to putty's format: First generate keys on RHEL: # ssh-keygen -t rsa Then put public key into authorizedkeys file: # cat publickey /.ssh.
Jun 03, 2019 How to Convert OpenSSH keys to Putty (.ppk) on Linux June 3, 2019 by Hayden James, in Blog Linux. PuTTYgen is an key generator for creating SSH keys for PuTTY. PuTTYgen is comparable in certain respects to the ssh-keygen tool. PuTTYgen can be used to create public and private key. You can generate an SSH key pair directly in cPanel, or you can generate the keys yourself and just upload the public one in cPanel to use with your hosting account. When generating SSH keys yourself under Linux, you can use the ssh-keygen command.
Jan 01, 2019 PuTTY is a free and open-source SSH and telnet client. It is primarily developed by Simon Tatham for Microsoft Windows but now it supports a wide variety of other operating systems. Public key authentication is a feature of PuTTY, in which, we can configure SSH Keys to allow password less logins to Linux machines from our PuTTY terminals. In this article, we are configuring SSH Keys using. How To Configure SSH Keys Authentication With PuTTY And Linux Server In 5 Quick Steps 1. Get the zip file with all PuTTY binaries. Generate a private and public key pair. Open PuTTYgen.exe, press Generate button, move mouse. Configure your Linux server (create user, save public key) For this.
This article provides steps for generating RSA keys by using PuTTYgen onWindows for secure SSH authentication with OpenSSH.
Generate keys
In Windows, use PuTTYgen to generate your public and private keys.
- If needed, download PuTTYgen from the PuTTY download page.(PuTTYgen might have been installed previously with PuTTY or WinSCP.)
- Launch the program, and then click the Generate button.The program generates the keys for you.
- Enter a unique key passphrase in the Key passphrase andConfirm passphrase fields.For additional information about using passphrases,see Log in with a SSH Private Key on Windows.
- Save the public and private keys by clicking the Save public keyand Save private key buttons.
- From the Public key for pasting into OpenSSH authorized_keys filefield at the top of the window, copy all the text (starting with ssh-rsa)to your clipboard by pressing Ctrl-C.You need this key available on your clipboard to paste eitherinto the public key tool in the Control Panel or directly into theauthorized keys on your cloud server.
Use the key pair
You can use the RSA key pair in the following ways.
Specify your SSH key when creating a new cloud server
When you create a cloud server, you can assign a public key from the list of keys.If your key is not already in the list, you may add it, and then assign it.
Add a new public key to the list
- Under Advanced Options on the Create Server page, click Manage SSHKeys.
- Select public key for the cloud server from the SSH Keys listand click Add Public Key.
- Enter the key name, select the region, and paste the entire publickey into the Public Key field. Then click Add Public Key.
- Go back to the Create Server page, and confirm that your key is listedin the SSH Key list.
Assign a public key
- Under Advanced Options on the Create Server page, select the publickey you want to use from the SSH key drop-down menu.
- When you are done specifying the all the other details for the server,click Create Server.
Assign your SSH Key to an existing cloud server
To make use of your newly generated RSA key pair, you must tell PuTTY touse it when connecting to your cloud server.
To edit the file (or create it), run the following command on the cloud server:
Paste the text onto its own line in the file.
You must have the key available in your clipboard to paste it. The key and itsassociated text (the ssh-rsa identified at the start and the comment at the end)must be on one line in the file. If the text is word-wrapped onto multiple linesan error might occur when connecting.
If you created the authorized_keys file, change its permissionsafter you’re done editing it by running the following command:
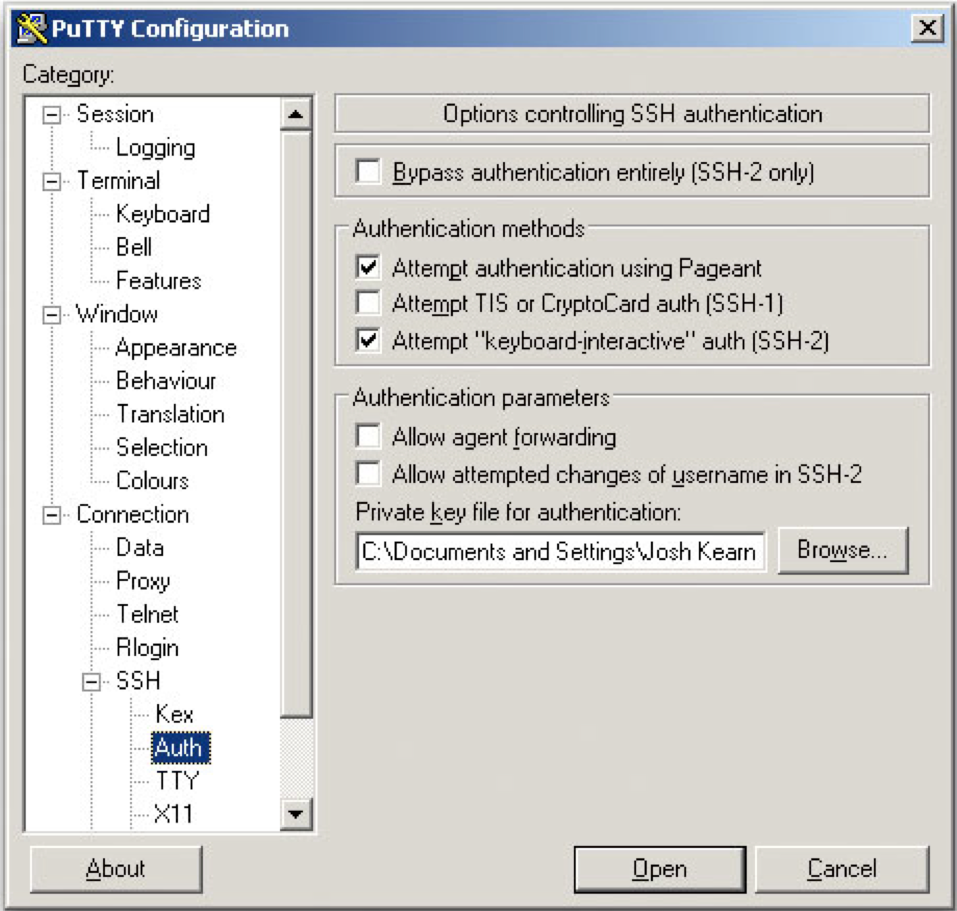
Open PuTTY, and go to the SSH > Auth section.
Browse to the location of the key file, and load the private key.
Go to the Session page, and save the session. This saves the configurationso that PuTTY uses the key every time that you connect to your cloudserver.
After you save your session, your key is loaded automatically when youconnect to your server.
Related article
Experience what Rackspace has to offer.
©2020 Rackspace US, Inc.
Except where otherwise noted, content on this site is licensed under a Creative Commons Attribution-NonCommercial-NoDerivs 3.0 Unported License
I am a new Ubuntu 18.04 LTS user and I would like to setup ssh public key authentication. How do I set up ssh keys based authentication on Ubuntu Linux 18.04 LTS server? How do I set up SSH keys on an Ubuntu Linux 18.04 LTS server? In Ubuntu 18.04 LTS, how do I set up public key authentication?Introduction: OpenSSH is a free and open source client/server technology for secure remote login. It is an implementation of the SSH protocol. OpenSSH divided into sshd (server) and various client tools such as sftp, scp, ssh and more. One can do remote login with OpenSSH either using password or combination of private and public keys named as public key based authentication. It is an alternative security method for user passwords. This method is recommended on a VPS, cloud, dedicated or even home-based server or laptop. This page shows how to set up SSH keys on Ubuntu 18.04 LTS server.
Ubuntu 18.04 Setup SSH Public Key Authentication
The procedure to set up secure ssh keys on Ubuntu 18.04:
- Create the key pair using ssh-keygen command.
- Copy and install the public key using ssh-copy-id command.
- Add yourself to sudo admin account on Ubuntu 18.04 server.
- Disable the password login for root account on Ubuntu 18.04.
Sample set up for SSH Keys on Ubuntu 18.04
/openssl-generate-rsa-key-without-passphrase.html.
Where,
- 202.54.1.55 – You store your public key on the remote hosts and you have an accounts on this Ubuntu Linux 18.04 LTS server.
- Linux/macbook laptop – Your private key stays on the desktop/laptop/computer (or local server) you use to connect to 202.54.1.55 server. Do not share or give your private file to anyone.
In public key based method you can log into remote hosts and server, and transfer files to them, without using your account passwords. Feel free to replace 202.54.1.55 and client names with your actual setup. Enough talk, let’s set up public key authentication on Ubuntu Linux 18.04 LTS.
How to create the RSA/ed25519 key pair on your local desktop/laptop
Open the Terminal and type following commands if .ssh directory does not exists:$ mkdir -p $HOME/.ssh
$ chmod 0700 $HOME/.ssh
Next generate a key pair for the protocol, run:$ ssh-keygen
OR$ ssh-keygen -t rsa 4096 -C 'My key for Linode server'
These days ED25519 keys are favored over RSA keys when backward compatibility is not needed:$ ssh-keygen -t ed25519 -C 'My key for Linux server # 42'
How to install the public key in Ubuntu 18.04 remote server
The syntax is as follows:ssh-copy-id your-user-name@your-ubuntu-server-name
ssh-copy-id -i ~/.ssh/file.pub your-user-name@your-ubuntu-server-name
For example:## for RSA KEY ##
ssh-copy-id -i $HOME/.ssh/id_rsa.pub user@202.54.1.55
## for ED25519 KEY ##
ssh-copy-id -i $HOME/.ssh/id_ed25519.pub user@202.54.1.55
## install SSH KEY for root user ##
ssh-copy-id -i $HOME/.ssh/id_ed25519.pub root@202.54.1.55
I am going to install ssh key for a user named vivek (type command on your laptop/desktop where you generated RSA/ed25519 keys):$ ssh-copy-id -i ~/.ssh/id_ed25519.pub vivek@202.54.1.55
Test it
Now try logging into the Ubuntu 18.04 LTS server, with ssh command from your client computer/laptop using ssh keys:$ ssh your-user@your-server-name-here
$ ssh vivek@202.54.1.55
What are ssh-agent and ssh-add, and how do I use them on Ubuntu 18.04?
To get rid of a passphrase for the current session, add a passphrase to ssh-agent (see ssh-agent command for more info) and you will not be prompted for it when using ssh or scp/sftp/rsync to connect to hosts with your public key. The syntax is as follows:$ eval $(ssh-agent)
Type the ssh-add command to prompt the user for a private key passphrase and adds it to the list maintained by ssh-agent command:$ ssh-add
Enter your private key passphrase. Now try again to log into vivek@202.54.1.55 and you will NOT be prompted for a password:$ ssh vivek@202.54.1.55
How to disable the password based login on a Ubuntu 18.04 server
Login to your server, type:## client commands ##
$ eval $(ssh-agent)
$ ssh-add
$ ssh vivek@202.54.1.55
Now login as root user:$ sudo -i
OR$ su -i
Edit sshd_config file:# vim /etc/ssh/sshd_config
OR# nano /etc/ssh/sshd_config
Find PermitRootLogin and set it as follows:PermitRootLogin no
Save and close the file. I am going to add a user named vivek to sudoers group on Ubuntu 18.04 server so that we can run sysadmin tasks:# adduser vivek sudo
Restart/reload the sshd service:# systemctl reload ssh
You can exit from all session and test it as follows:$ ssh vivek@202.54.1.55
## become root on server for sysadmin task ##
$ sudo -i
How do I add or replace a passphrase for an existing private key?
To to change your SSH passphrase type the following command:$ ssh-keygen -p
How do I backup my existing private/public SSH keys
Just copy files to your backup server or external USB pen/hard drive:
How do I protect my ssh keys?
- Always use a strong passphrase.
- Do not share your private keys anywhere online or store in insecure cloud storage or gitlab/github servers.
- Restrict privileges of the account.
Putty Use Ssh Key
Tip: Create and setup an OpenSSH config file to create shortcuts for servers
See how to create and use an OpenSSH ssh_config file for more info.
How do I secure my OpenSSH server?
Add Ssh Key To Putty
See “OpenSSH Server Best Security Practices” for more info.
Conclusion
You learned how to create and install ssh keys for SSH key-based authentication for Ubuntu Linux 18.04 LTS server. See OpenSSH server documents here and here for more info.
ADVERTISEMENTS