Gpg Option For Generate Key
Please login with same user,which is used to create gpg keys. 1.We will export both our public key and private key as follows: user$ gpg -export -a -o mypublickey.txt user@replaceurmail.com user$ gpg -export-secret-key -a -o myprivatekey.txt user@replaceurmail.com user$ ls my. After your keypair is created you should immediately generate a revocation certificate for the primary public key using the option -gen-revoke. If you forget your passphrase or if your private key is compromised or lost, this revocation certificate may be published to notify others that the public key should no longer be used.
- Gpg Invalid Option --full-generate-key
- Gpg Option For Generate Key File
- Gpg Option For Generate Key Windows
Encryption is a process of embedding plain text data in such a way that it cannot be decoded by outsiders. It is necessary to encrypt data to prevent misuse. The GNU Privacy Guard (GPG) application allows you to encrypt and decrypt information. It is based on the use of a pair of keys, one public and one private (or secret). Data encrypted with one key can only be decrypted with the other. To encrypt a message to you, someone would use your public key to create a message that could only be unlocked with your private key. To sign information, you would lock it with your private key, allowing anyone to verify that it came from you by unlocking it with your public key.
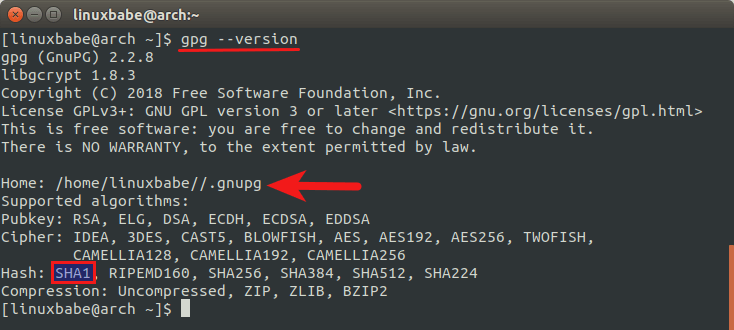
Modern Linux distributions have gpg already installed on them. If not present, install it.
on Centos
on Ubuntu
1) Create gpg key
When installing gnupg package, we need to understand the concept to use gpg as well.
Generating a new keypair
To encrypt your communication, the first thing to do is to create a new keypair. GPG is able to create several types of keypairs, but a primary key must be capable of making signatures.
uid:Please take a note about the USER-ID mentioned in the result. We will use its value to do some operation.pub:It represents the public key. The key-id is BAC361F1. Yours will be differentsub:It represents subkeys, goes along with the primary key. Commonly, it is used to encryption.
Your prompt can be handled for a very long time without finishing if you see the message below
'Not enough random bytes available. Please do some other work to give
the OS a chance to collect more entropy! (Need 285 more bytes)'
The problem is caused by the lack of entropy (or random system noise). So cancel the process and check the available entropy
You can see it is not enough. We can install a package to solve the lack of entropy with rngd which is a random number generator utility used to check immediately the available entropy
Now can start again with the gpg --gen-key command and the process will be fine. We have only installed it without anything else. In certain distributions, you need to use rngd before the gpg process.
3) Generating a revocation certificate
After your keypair is created you should immediately generate a revocation certificate to revoke your public key if your private key has been compromised in any way or if you lose it. Create it when you create your key. The process requires your private key, passphrase.
The argument BAC361F1 is the key ID. It must be a key specifier, either the key ID of your primary keypair or any part of a user ID that identifies your keypair like my_name@linoxide.com. The generated certificate will be saved in revoke_key.asc file. Store it where others can't access it because anybody having access to it can revoke your key, rendering it useless. If the --output option is omitted, the result will be placed on standard output.
4) Making an ASCII armored version of your public key
Some keyservers allow you to paste an ASCII armored version of your public key in order to upload it directly. This method is most preferred because the key comes directly from the user who can see that the key has been successfully uploaded.
5) Exchanging keys
In order to communicate with others, you must exchange public keys. To do it, you must be able to list your keys. There is some commands to list your public keyring
gpg --list-keys:List all keys from the public keyrings, or just the keys given on the command line.gpg --list-secret-keys:List all keys from the secret keyrings or just the ones given on the command linegpg --list-sigs:Same as --list-keys, but the signatures are listed too.
Export a public key
Now that you have generated a key pair, the next step is to publish your public key on internet ( Keyservers ) so that other person can use it to send you a message. You can use either the key ID or any part of the user ID may be used to identify the key to export. There are two commands but with the first command, the key is exported in a binary format and can be inconvenient when it is sent through email or published on a web page. So, we will use the second command for ASCII armored method.
Apache generate csr private key. The output will be redirected to my_pubkey.gpg file which has the content of the public key to provide for communication.
Submit your public keys to a keyserver
Once you have this ASCII-armored public key, you can manually paste it into a form at a public key server like pgp.mit.edu
Because someone seems to have sent you their public key, there's no reason to trust that it's from that person unless you have validated it.

Import a public key
As others persons can use your public key to send you a message, you can import public from people you trust in to communicate with them.
Conclusion
Now we have notions on the principles to use and generate a public key. You know how GnuPG is functioning and you can use it for secure communication. GPG encryption is only useful when both parties use good security practices and are vigilant.
Read Also:
Encryption/decryption commands
- To encrypt a plaintext file with the recipient's public key:
- To sign a plaintext file with your secret key:
- To sign a plaintext file with your secret key and have the outputreadable to people without running GPG first:
- To sign a plaintext file with your secret key, and then encrypt itwith the recipient's public key:
- To decrypt an encrypted file, or to check the signature integrityof a signed file:
Key management commands
- To generate your own unique public/secret key pair:
- To add a public or secret key file's contents to your public orsecret key ring:
- To extract (copy) a key from your public or secret key ring:
or
- To view the contents of your public key ring:
- To view the 'fingerprint' of a public key, to help verify it overthe telephone with its owner:
- To view the contents and check the certifying signatures of yourpublic key ring:
- To edit a key:
- To remove a key or just a userid from your public key ring:
- To permanently revoke your own key, issuing a key compromise certificate:
- To disable or re-enable a public key on your own public key ring:
or
Esoteric commands
Gpg Invalid Option --full-generate-key
- To create a signature certificate that is detached from the document:
- To detach a signature certificate from a signed message
Gpg Option For Generate Key File
Command options that can be used in combination with other command options
Gpg Option For Generate Key Windows
- To produce a ciphertext file in ASCII format, just add the -aoption when encrypting or signing a message or extracting a key:
- To specify a recipient, add the -r option followed by a user id:
- To specify an output file, add the -o option followed by a filename: