Generate Client Cert And Key
Jun 01, 2018 What is a Self-Signed TLS Certificate? Create a 4096 bit RSA key for use with the certificate. RSA 2048 is the default on more recent versions of OpenSSL but to be sure of the key size, you should specify it during creation.-x509: Create a self-signed certificate. For example, instead of generating the client certificate and keys on the server, we could have had the client generate its own private key locally, and then submit a Certificate Signing Request (CSR) to the key-signing machine. In turn, the key-signing machine could have processed the CSR and returned a signed certificate to the client. Mar 29, 2016 In the same way we extracted the server’s public key, we can extract the client’s public key with the following command. This generates a file called client.cert containing the public certificate from the client.jks keystore.
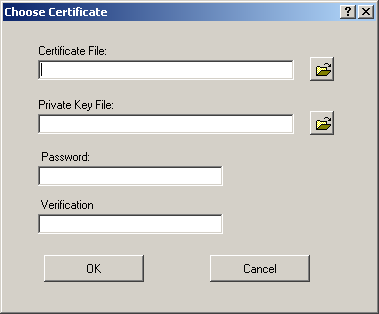
Look for a folder called REQUEST or 'Certificate Enrollment Request Certificates. Select the private key that you wish to backup. Right click on the file and choose All Tasks Export. The certificate export wizard will start, please click Next to continue. In the next window select Yes, export the private key and click Next. Update: We should sign the CertificateSignRequest with the sign operation with your CA server. Enterprise certificate: If you are using an enterprise certificate solution, generate a client certificate with the common name value format 'name@yourdomain.com', rather than the 'domain name username' format. Create a self-signed root certificate, export the public key, and generate client certificates using PowerShell on Windows 10 or Windows Server 2016.
Syntax
Description
The New-SelfSignedCertificate cmdlet creates a self-signed certificate for testing purposes.Using the CloneCert parameter, a test certificate can be created based on an existing certificate with all settings copied from the original certificate except for the public key.The cmdlet creates a new key of the same algorithm and length.
Delegation may be required when using this cmdlet with Windows PowerShell remoting and changing user configuration.
Examples
EXAMPLE 1
This example creates a self-signed SSL server certificate in the computer MY store with the subject alternative name set to www.fabrikam.com, www.contoso.com and Subject and Issuer name set to www.fabrikam.com.
EXAMPLE 2
This example creates a copy of the certificate specified by the CloneCert parameter and puts it in the computer MY store.
EXAMPLE 3
This example creates a self-signed S/MIME certificate in the user MY store.The certificate uses the default provider, which is the Microsoft Software Key Storage Provider.The certificate uses an RSA asymmetric key with a key size of 2048 bits.This certificate has the subject alternative names of patti.fuller@contoso.com as RFC822 and pattifuller@contoso.com as Principal Name.
This command does not specify the NotAfter parameter.Therefore, the certificate expires in one year.
EXAMPLE 4
This example creates a self-signed client authentication certificate in the user MY store.The certificate uses the default provider, which is the Microsoft Software Key Storage Provider.The certificate uses an RSA asymmetric key with a key size of 2048 bits.The certificate has a subject alternative name of pattifuller@contoso.com.
The certificate expires in one year.
EXAMPLE 5
This example creates a self-signed client authentication certificate in the user MY store.The certificate uses the default provider, which is the Microsoft Software Key Storage Provider.The certificate uses an elliptic curve asymmetric key and the curve parameters nist256, which creates a 256-bit key.The subject alternative name is pattifuller@contoso.com.
The certificate expires in one year.
EXAMPLE 6
This example creates a self-signed client authentication certificate in the user MY store.The certificate uses the Microsoft Platform Crypto Provider.This provider uses the Trusted Platform Module (TPM) of the device to create the asymmetric key.The key is an RSA 2048-bit key that cannot be exported.The subject alternative name is pattifuller@contoso.com.The certificate expires in one year.
EXAMPLE 7
This example creates a self-signed client authentication certificate in the user MY store.The certificate uses the default provider, which is the Microsoft Software Key Storage Provider.The certificate uses an RSA asymmetric key with a key size of 2048 bits.The subject alternative name is pattifuller@contoso.com.
This command specifies a value for NotAfter.The certificate expires in six months.
EXAMPLE 8
This example creates a self-signed S/MIME certificate in the user MY store.The certificate uses the default provider, which is the Microsoft Software Key Storage Provider.The certificate uses an RSA asymmetric key with a key size of 2048 bits.This certificate has the subject alternative names of patti.fuller@contoso.com and pattifuller@contoso.com both as RFC822.
This command does not specify the NotAfter parameter.Therefore, the certificate expires in one year.
EXAMPLE 9
This example creates a self-signed SSL server certificate with Subject and Issuer name set to localhost and with subject alternative name set to IPAddress 127.0.0.1 and ::1 via TextExtension.
Parameters
Indicates that this cmdlet uses RSA-PSS (PKCSv2.1) or an elliptic curve cryptography (ECC) equivalent.If you do not specify this parameter, the cmdlet uses the default, RSA-PSS (PKCSv1.5) or an ECC equivalent.
| Type: | SwitchParameter |
| Position: | Named |
| Default value: | None |
| Accept pipeline input: | False |
| Accept wildcard characters: | False |
Specifies the certificate store in which to store the new certificate.If the current path is Cert:CurrentUser or Cert:CurrentUserMy, the default store is Cert:CurrentUserMy.If the current path is Cert:LocalMachine or Cert:LocalMachineMy, the default store is Cert:LocalMachineMy.Otherwise, you must specify Cert:CurrentUserMy or Cert:LocalMachineMy for this parameter.This parameter does not support other certificate stores.
| Type: | String |
| Position: | Named |
| Default value: | None |
| Accept pipeline input: | False |
| Accept wildcard characters: | False |
Identifies the certificate to copy when creating a new certificate.The certificate being cloned can be identified by an X509 certificate or the file path in the certificate provider.When this parameter is used, all fields and extensions of the certificate will be inherited except the public key, a new key of the same algorithm and length will be created, and the NotAfter and NotBefore fields.The default validity period will be the same as the certificate to copy, except that the NotBefore field will be set to ten minutes in the past.
| Type: | Certificate |
| Position: | Named |
| Default value: | None |
| Accept pipeline input: | True (ByValue) |
| Accept wildcard characters: | False |
Prompts you for confirmation before running the cmdlet.
| Type: | SwitchParameter |
| Aliases: | cf |
| Position: | Named |
| Default value: | False |
| Accept pipeline input: | False |
| Accept wildcard characters: | False |

Specifies the name of the container in which this cmdlet stores the key for the new certificate.
When you create a key, a trailing asterisk (*) indicates that the rest of the container name string is a prefix.An appended GUID string makes the container name unique.
When you use an existing key, the container name must identify an existing key.You may also have to specify the provider.
| Type: | String |
| Position: | Named |
| Default value: | None |
| Accept pipeline input: | False |
| Accept wildcard characters: | False |
Specifies how the public key parameters for an elliptic curve key are represented in the new certificate.The acceptable values for this parameter are:
- CurveParameters
- CurveName
- None (default)
The default value, None, indicates that this cmdlet uses the default value from the underlying key storage provider (KSP).This parameter is not supported with the RSA algorithm or with cryptographic service providers (CSPs).
| Type: | CurveParametersExportType |
| Accepted values: | None, CurveParameters, CurveName |
| Position: | Named |
| Default value: | None |
| Accept pipeline input: | False |
| Accept wildcard characters: | False |
Specifies one or more DNS names to put into the subject alternative name extension of the certificate when a certificate to be copied is not specified via the CloneCert parameter.The first DNS name is also saved as the Subject Name.If no signing certificate is specified, the first DNS name is also saved as the Issuer Name.
| Type: | String[] |
| Position: | Named |
| Default value: | None |
| Accept pipeline input: | False |
| Accept wildcard characters: | False |
Indicates that this cmdlet uses an existing key.If you do not specify this parameter, this cmdlet creates a new key.Creating a certificate from an existing key creates a new key with a new container.
When you use an existing key, specify values for the Container parameter, the Provider parameter, and the CertStoreLocation parameter.CertStoreLocation determines the context.The context is user or computer.
| Type: | SwitchParameter |
| Position: | Named |
| Default value: | None |
| Accept pipeline input: | False |
| Accept wildcard characters: | False |
Specifies an array of certificate extensions, as X509Extension objects, that this cmdlet includes in the new certificate.
| Type: | X509Extension[] |
| Position: | Named |
| Default value: | None |
| Accept pipeline input: | False |
| Accept wildcard characters: | False |
Specifies a friendly name for the new certificate.
| Type: | String |
| Position: | Named |
| Default value: | None |
| Accept pipeline input: | False |
| Accept wildcard characters: | False |
Specifies how a hardware key associated with the new certificate may be used.This parameter applies only when you specify the Microsoft Platform Crypto Provider.The acceptable values for this parameter are:
- None (default)
- SignatureKey
- EncryptionKey
- GenericKey
- StorageKey
- IdentityKey
The default value, None, indicates that this cmdlet uses the default value from the underlying KSP.
| Type: | HardwareKeyUsage[] |
| Accepted values: | None, SignatureKey, EncryptionKey, GenericKey, StorageKey, IdentityKey |
| Position: | Named |
| Default value: | None |
| Accept pipeline input: | False |
| Accept wildcard characters: | False |
Specifies the name of the hash algorithm to use to sign the new certificate.The default hash algorithm depends on the provider that stores the private key used to sign the new certificate.
| Type: | String |
| Position: | Named |
| Default value: | None |
| Accept pipeline input: | False |
| Accept wildcard characters: | False |
Specifies the name of the algorithm that creates the asymmetric keys that are associated with the new certificate.Available asymmetric key algorithms are RSA and Elliptic Curve Digital Signature Algorithms (ECDSA).
The elliptic curve algorithm syntax is the following:
ECDSA_curvename
To obtain a value for curvename, use the certutil -displayEccCurve command.
Valid curve names contain a value in the Curve OID column in the output of the certutil -displayEccCurve command.
| Type: | String |
| Position: | Named |
| Default value: | None |
| Accept pipeline input: | False |
| Accept wildcard characters: | False |
Specifies a description for the private key that is associated with the new certificate.
| Type: | String |
| Position: | Named |
| Default value: | None |
| Accept pipeline input: | False |
| Accept wildcard characters: | False |
Specifies the policy that governs the export of the private key that is associated with the certificate.The acceptable values for this parameter are:
- Exportable
- ExportableEncrypted (default)
- NonExportable
The default value of ExportableEncrypted is not compatible with KSP and CSPs that do not allow key export.These include the Microsoft Smart Card Key Storage Provider and the Microsoft Platform Crypto Key Storage Provider.Specify NonExportable for providers that do not allow key export.
| Type: | KeyExportPolicy[] |
| Accepted values: | NonExportable, ExportableEncrypted, Exportable |
| Position: | Named |
| Default value: | None |
| Accept pipeline input: | False |
| Accept wildcard characters: | False |
Specifies a friendly name for the private key that is associated with the new certificate.
| Type: | String |
| Position: | Named |
| Default value: | None |
| Accept pipeline input: | False |
| Accept wildcard characters: | False |
Specifies the length, in bits, of the key that is associated with the new certificate.
| Type: | Int32 |
| Position: | Named |
| Default value: | None |
| Accept pipeline input: | False |
| Accept wildcard characters: | False |
Specifies the file system location where this cmdlet stores the private keys associated with the new certificate.Specify this parameter only when you specify the Microsoft Platform Crypto Provider.
| Type: | String |
| Position: | Named |
| Default value: | None |
| Accept pipeline input: | False |
| Accept wildcard characters: | False |
Specifies the level of protection required to access the private key that is associated with the certificate.The acceptable values for this parameter are:
- Protect
- ProtectHigh
- ProtectFingerPrint
- None (default)
The default value, None, indicates that this cmdlet uses the default value from the underlying KSP or CSP.For most KSPs and CSPs, the default means that no user interface is required to create and use the private key.A user interface is required if the provider always requires a user interface, such as a smart card, or if the default configuration of the provider has been changed.
| Type: | KeyProtection[] |
| Accepted values: | None, Protect, ProtectHigh, ProtectFingerPrint |
| Position: | Named |
| Default value: | None |
| Accept pipeline input: | False |
| Accept wildcard characters: | False |
Specifies whether the private key associated with the new certificate can be used for signing, encryption, or both.The acceptable values for this parameter are:
- KeyExchange
- Signature
- None (default)
The default value, None, indicates that this cmdlet uses the default value from the underlying CSP.
If the private key is managed by a legacy CSP, the value is KeyExchange or Signature.If the key is managed by a Cryptography Next Generation (CNG) KSP, the value is None.
| Type: | KeySpec |
| Accepted values: | None, KeyExchange, Signature |
| Position: | Named |
| Default value: | None |
| Accept pipeline input: | False |
| Accept wildcard characters: | False |
Specifies the key usages set in the key usage extension of the certificate.The acceptable values for this parameter are:
- CertSign
- CRLSign
- DataEncipherment
- DecipherOnly
- DigitalSignature
- EncipherOnly
- KeyAgreement
- KeyEncipherment
- None (default)
- NonRepudiation
The value, None, indicates that this cmdlet does not include the KeyUsage extension in the new certificate.
| Type: | KeyUsage[] |
| Accepted values: | None, EncipherOnly, CRLSign, CertSign, KeyAgreement, DataEncipherment, KeyEncipherment, NonRepudiation, DigitalSignature, DecipherOnly |
| Position: | Named |
| Default value: | DigitalSignature,KeyEncipherment |
| Accept pipeline input: | False |
| Accept wildcard characters: | False |
Specifies the key usages for the key usages property of the private key.The acceptable values for this parameter are:
- All
- Decrypt
- KeyAgreement
- None (default)
- Sign
The default value, None, indicates that this cmdlet uses the default value from the underlying KSP.
| Type: | KeyUsageProperty[] |
| Accepted values: | None, Decrypt, Sign, KeyAgreement, All |
| Position: | Named |
| Default value: | None |
| Accept pipeline input: | False |
| Accept wildcard characters: | False |
Specifies the date and time, as a DateTime object, that the certificate expires.To obtain a DateTime object, use the Get-Date cmdlet.The default value for this parameter is one year after the certificate was created.
| Type: | DateTime |
| Position: | Named |
| Default value: | None |
| Accept pipeline input: | False |
| Accept wildcard characters: | False |
Specifies the date and time, as a DateTime object, when the certificate becomes valid.The default value for this parameter is 10 minutes before the certificate was created.
| Type: | DateTime |
| Position: | Named |
| Default value: | None |
| Accept pipeline input: | False |
| Accept wildcard characters: | False |
Specifies the personal identification number (PIN) used to access the private key of the new certificate.
| Type: | SecureString |
| Position: | Named |
| Default value: | None |
| Accept pipeline input: | False |
| Accept wildcard characters: | False |
Specifies the name of the KSP or CSP that this cmdlet uses to create the certificate. See Cryptographic Providers for more information.Some acceptable values include:
- Microsoft Software Key Storage Provider
- Microsoft Smart Card Key Storage Provider
- Microsoft Platform Crypto Provider
- Microsoft Strong Cryptographic Provider
- Microsoft Enhanced Cryptographic Provider v1.0
- Microsoft Enhanced RSA and AES Cryptographic Provider
- Microsoft Base Cryptographic Provider v1.0
- The name of a third party KSP or CSP
| Type: | String |
| Position: | Named |
| Default value: | None |
| Accept pipeline input: | False |
| Accept wildcard characters: | False |
Specifies the name of the smart card reader on which to store the private key for the new certificate.
| Type: | String |
| Position: | Named |
| Default value: | None |
| Accept pipeline input: | False |
| Accept wildcard characters: | False |
Specifies the private key security descriptor as a FileSecurity object.Read access is required to use the private key.This parameter does not apply to providers that do not support security descriptors on private keys, including the smart card CSP and smart card KSP.
| Type: | FileSecurity |
| Position: | Named |
| Default value: | None |
| Accept pipeline input: | False |
| Accept wildcard characters: | False |
Specifies a serial number, as a hexadecimal string, that is associated with the new certificate.If you do not specify this parameter, this cmdlet assigns a pseudo-randomly generated 16 byte value.
| Type: | String |
| Position: | Named |
| Default value: | None |
| Accept pipeline input: | False |
| Accept wildcard characters: | False |
Specifies a Certificate object with which this cmdlet signs the new certificate.This value must be in the Personal certificate store of the user or device.This cmdlet must have read access to the private key of the certificate.
| Type: | Certificate |
| Position: | Named |
| Default value: | None |
| Accept pipeline input: | False |
| Accept wildcard characters: | False |
Specifies the PIN that is required to access the private key of the certificate that is used to sign the new certificate.
| Type: | SecureString |
| Position: | Named |
| Default value: | None |
| Accept pipeline input: | False |
| Accept wildcard characters: | False |
Specifies the name of the smart card reader that is used to sign the new certificate.
| Type: | String |
| Position: | Named |
| Default value: | None |
| Accept pipeline input: | False |
| Accept wildcard characters: | False |
Indicates that the new certificate includes available encryption algorithms to a Secure/Multipurpose Internet Mail Extensions (S/MIME) capabilities extension.
| Type: | SwitchParameter |
| Position: | Named |
| Default value: | None |
| Accept pipeline input: | False |
| Accept wildcard characters: | False |
Specifies the string that appears in the subject of the new certificate.This cmdlet prefixes CN= to any value that does not contain an equal sign.For multiple subject relative distinguished names (also known as RDNs), separate each subject relative distinguished name with a comma (,).If the value of the relative distinguished name contains commas, separate each subject relative distinguished name with a semicolon (;).
| Type: | String |
| Position: | Named |
| Default value: | None |
| Accept pipeline input: | False |
| Accept wildcard characters: | False |
Specifies an array of object identifier (also known as OID) strings that identify default extensions to be removed from the new certificate.
| Type: | String[] |
| Position: | Named |
| Default value: | None |
| Accept pipeline input: | False |
| Accept wildcard characters: | False |
Indicates that this cmdlet signs the new certificate by using a built-in test certificate.This cmdlet adds the built-in test certificate to the intermediate certification authority (CA) certificate store of the device.
This parameter is for test purposes only.The private key of the test root certificate is essentially public.
| Type: | SwitchParameter |
| Position: | Named |
| Default value: | None |
| Accept pipeline input: | False |
| Accept wildcard characters: | False |
Specifies an array of certificate extensions, as strings, which this cmdlet includes in the new certificate.Each string must employ one of the following formats:
oid=base64String, where oid is the object identifier of the extension and base64String is a value that you provide.After decoding base64String, the value must be valid Abstract Syntax Notation One (ASN.1).For more information, see Abstract Syntax Notation One (ASN.1): Specification of basic notation.
oid={hex}hexidecimalString, where oid is the object identifier of the extension and hexidecimalString is a value that you provide.After decoding hexidecimalString, the value must be valid ASN.1.
oid={text}String, where oid is the object identifier of the extension and String is a value that you provide.String must contain a textual representation of the extension value in a format specific to each object ID.When String is processed, it will be encoded into an ASN.1 extension value before being placed into the new certificate as an extension.
To specify that an extension is critical, insert {critical} immediately following oid= in any of the previous cases.
The object identifiers of some common extensions are as follows:
- Application Policy.1.3.6.1.4.1.311.21.10
- Application Policy Mappings.1.3.6.1.4.1.311.21.11
- Basic Constraints.2.5.29.19
- Certificate Policies.2.5.29.32
- Enhanced Key Usage.2.5.29.37
- Name Constraints.2.5.29.30
- Policy Mappings.2.5.29.33
- Subject Alternative Name.2.5.29.17
Application Policy1.3.6.1.4.1.311.21.10={text}token=value&token=value…The tokens have the following possible values:
- Flags.0xhexidecimalNumber
- GUID.A globally unique ID, such as this example: f7c3ac41-b8ce-4fb4-aa58-3d1dc0e36b39
- Notice.Text notice
- OID.Object identifier in dotted decimal notation, such as this example: 1.2.3.4.5
- URL.The URL of a host, such as this example: http://computer07.contoso.com
To specify an Application Policy extension, specify the first object identifier, followed by zero or more other token=value entries.These entries are subordinate to the preceding object identifier.Specify subsequent object identifiers, each followed by its subordinate token=value entries.
Application Policy Mappings1.3.6.1.4.1.311.21.11={text}oid=oid&oid=oid…
Certificate Policies2.5.29.32={text}token=value&token=value…The tokens have the following possible values:
- Flags.0xhexidecimalNumber
- GUID.A globally unique ID, such as this example: f7c3ac41-b8ce-4fb4-aa58-3d1dc0e36b39
- Notice.Text notice
- OID.Object ID in dotted decimal notation, such as this example: 1.2.3.4.5
- URL.The URL of a host, such as this example: http://computer07.contoso.com
To specify a Certificate Policies extension, follow the same syntax as an Application Policy extension.
Enhanced Key Usage Object Identifiers2.5.29.37={text}oid,oid…These key usages have the following object identifiers:
- Client Authentication.1.3.6.1.5.5.7.3.2
- Server Authentication.1.3.6.1.5.5.7.3.1
- Secure Email.1.3.6.1.5.5.7.3.4
- Code Signing.1.3.6.1.5.5.7.3.3
- Timestamp Signing.1.3.6.1.5.5.7.3.8
Name Constraints2.5.29.30={text}subtree=subtreeValue&token=value&token=value& …&subtree=subtreeValue&token=value&token=value…The subtreeValue can have the following values:
- Include.Permitted names
- Exclude.Excluded names
The tokens have the following possible values:
- DirectoryName.CN=Name,DC=Domain,DC=com
- DNS.A computer name in the following format: computer.contoso.com
- Email.An email address, such as this example: admin@contoso.com
- IPAddress.IPV4 address,IPV4 subnet mask or IPV6 address,IPV6 subnet mask
- RegisteredID.ID in dotted decimal notation, such as this example: 1.2.3.4.5
- UPN.A user principal name in the following format: admin@contoso.com
- URL.The URL of a host, such as this example: http://computer07.contoso.com/index.html
Policy Mapping2.5.29.33={text}oid=oid&oid=oid…
Subject Alternative Name Syntax2.5.29.17={text}token=value&token=value…The tokens have the following possible values:
- UPN.A user principal name in the following format: admin@contoso.com
- Email.An email address, such as this example: admin@contoso.com
- DNS.A computer name in the following format: computer.contoso.com
- DirectoryName.CN=Name,DC=Domain,DC=com
- URL.The URL of a host, such as this example: http://computer07.contoso.com/index.html
- IPAddress.An IP address
- RegisteredID.ID in dotted decimal notation, such as this example: 1.2.3.4.5
- GUID.A globally unique ID, such as this example: f7c3ac41-b8ce-4fb4-aa58-3d1dc0e36b39
| Type: | String[] |
| Position: | Named |
| Default value: | None |
| Accept pipeline input: | False |
| Accept wildcard characters: | False |
Specifies the type of certificate that this cmdlet creates.The acceptable values for this parameter are:
- CodeSigningCert
- Custom
- DocumentEncryptionCert
- DocumentEncryptionCertLegacyCsp
- SSLServerAuthentication (default)
| Type: | CertificateType |
| Accepted values: | Custom, CodeSigningCert, DocumentEncryptionCert, SSLServerAuthentication, DocumentEncryptionCertLegacyCsp |
| Position: | Named |
| Default value: | None |
| Accept pipeline input: | False |
| Accept wildcard characters: | False |
Shows what would happen if the cmdlet runs.The cmdlet is not run.
| Type: | SwitchParameter |
| Aliases: | wi |
| Position: | Named |
| Default value: | False |
| Accept pipeline input: | False |
| Accept wildcard characters: | False |
Inputs
Microsoft.CertificateServices.Commands.Certificate
The Certificate object can either be provided as a Path object to a certificate or an X509Certificate2 object.
Outputs
System.Security.Cryptography.X509Certificates.X509Certificate2
An X509Certificate2 object for the certificate that has been created.
Related Links
5.3.2 Creating SSL Certificates and Keys Using openssl
This section describes how to use the openssl command to set up SSL certificate and key files for use by MySQL servers and clients. The first example shows a simplified procedure such as you might use from the command line. The second shows a script that contains more detail. The first two examples are intended for use on Unix and both use the openssl command that is part of OpenSSL. The third example describes how to set up SSL files on Windows.
There are easier alternatives to generating the files required for SSL than the procedure described here: Let the server autogenerate them or use the mysql_ssl_rsa_setup program. See Section 5.3.1, “Creating SSL and RSA Certificates and Keys using MySQL”.
Whatever method you use to generate the certificate and key files, the Common Name value used for the server and client certificates/keys must each differ from the Common Name value used for the CA certificate. Otherwise, the certificate and key files will not work for servers compiled using OpenSSL. A typical error in this case is:
Example 1: Creating SSL Files from the Command Line on Unix
The following example shows a set of commands to create MySQL server and client certificate and key files. You will need to respond to several prompts by the openssl commands. To generate test files, you can press Enter to all prompts. To generate files for production use, you should provide nonempty responses.
After generating the certificates, verify them:
You should see a response like this:
To see the contents of a certificate (for example, to check the range of dates over which a certificate is valid), invoke openssl like this:
Now you have a set of files that can be used as follows:
ca.pem: Use this to set thessl_casystem variable on the server side and the--ssl-caoption on the client side. (The CA certificate, if used, must be the same on both sides.)server-cert.pem,server-key.pem: Use these to set thessl_certandssl_keysystem variables on the server side.client-cert.pem,client-key.pem: Use these as the arguments to the--ssl-certand--ssl-keyoptions on the client side.
For additional usage instructions, see Section 5.1, “Configuring MySQL to Use Encrypted Connections”.
Example 2: Creating SSL Files Using a Script on Unix
Here is an example script that shows how to set up SSL certificate and key files for MySQL. After executing the script, use the files for SSL connections as described in Section 5.1, “Configuring MySQL to Use Encrypted Connections”.
Download OpenSSL for Windows if it is not installed on your system. An overview of available packages can be seen here:
Choose the Win32 OpenSSL Light or Win64 OpenSSL Light package, depending on your architecture (32-bit or 64-bit). The default installation location will be C:OpenSSL-Win32 or C:OpenSSL-Win64, depending on which package you downloaded. The following instructions assume a default location of C:OpenSSL-Win32. Modify this as necessary if you are using the 64-bit package.
If a message occurs during setup indicating '...critical component is missing: Microsoft Visual C++ 2008 Redistributables', cancel the setup and download one of the following packages as well, again depending on your architecture (32-bit or 64-bit):
Visual C++ 2008 Redistributables (x86), available at:
Visual C++ 2008 Redistributables (x64), available at:
After installing the additional package, restart the OpenSSL setup procedure.
During installation, leave the default C:OpenSSL-Win32 as the install path, and also leave the default option 'Copy OpenSSL DLL files to the Windows system directory' selected.
Generate Client Cert And Key Code
When the installation has finished, add C:OpenSSL-Win32bin to the Windows System Path variable of your server (depending on your version of Windows, the following path-setting instructions might differ slightly):
On the Windows desktop, right-click the My Computer icon, and select Properties.
Select the Advanced tab from the System Properties menu that appears, and click the button.
Under System Variables, select Path, then click the button. The Edit System Variable dialogue should appear.
Add
';C:OpenSSL-Win32bin'to the end (notice the semicolon).Press OK 3 times.
Check that OpenSSL was correctly integrated into the Path variable by opening a new command console (Start>Run>cmd.exe) and verifying that OpenSSL is available:
Generate Client From Wsdl
After OpenSSL has been installed, use instructions similar to those from Example 1 (shown earlier in this section), with the following changes:
Change the following Unix commands:
On Windows, use these commands instead:
When a
'character is shown at the end of a command line, this'character must be removed and the command lines entered all on a single line.
Generate Client Cert And Key Download
After generating the certificate and key files, to use them for SSL connections, see Section 5.1, “Configuring MySQL to Use Encrypted Connections”.